Supply Chain Security Services in USA
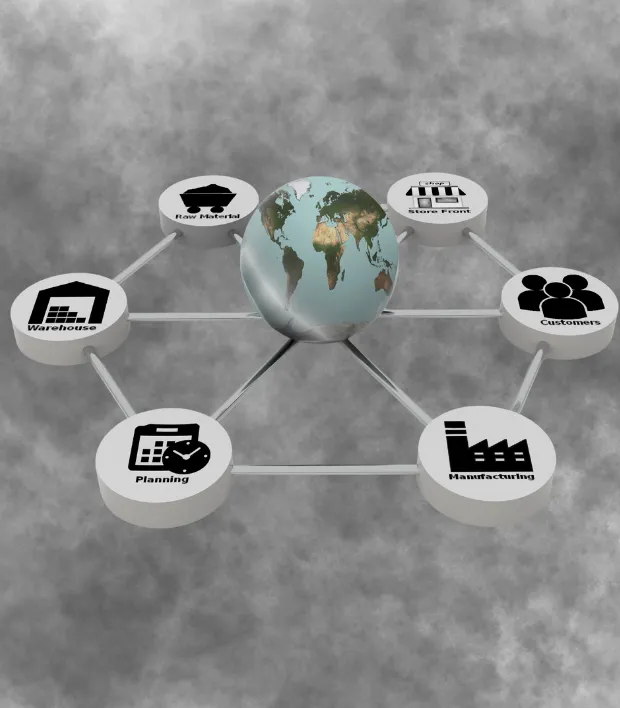
Supply chain systems are vulnerable to cyberattacks, data breaches, and operational disruptions. We provide advanced supply chain security solutions that identify risks, protect sensitive information, and ensure uninterrupted business operations. Our experts help organizations secure suppliers, partners, and internal workflows, enabling safe, compliant, and resilient supply chain communication for businesses of all sizes.
Get In Touch
About Our Supply Chain Security Services

Supply chain security ensures that every link in your business network, from suppliers and partners to internal operations, is protected against cyber threats. Vulnerabilities in the supply chain can lead to data breaches, financial loss, and operational disruption, making proactive security critical for modern businesses.
Our supply chain security services focus on assessing risks, securing communication channels, and monitoring all digital interactions between partners, vendors, and internal systems. We help organizations implement robust access controls, encryption, and compliance measures to prevent unauthorized access and safeguard sensitive data throughout the supply chain.
These services are designed for businesses of all sizes across industries, including manufacturing, logistics, healthcare, and finance. By securing the supply chain, organizations can maintain operational continuity, protect valuable information, and build trust with partners and clients alike.

Ready to Secure Your Business?
Ready to make your digital world impervious to cyber threats? Don’t wait. Contact us today, and let’s embark on a journey to fortify your digital assets.
services
Supply Chain Security Services
Our supply chain security services protect organizations from cyber risks, operational disruptions, and data breaches across their entire supply ecosystem. We secure communication, systems, and processes to ensure safe, compliant, and resilient supply chain operations.
Managed Security
Comprehensive monitoring and management of all supply chain systems reduce cyber risk. Threats are detected and mitigated in real time. This ensures operational continuity and secure workflows across partners.
Reputation Monitoring
We track and protect the organization’s digital reputation within the supply chain. Potential risks from partner or vendor interactions are identified early. Businesses can maintain trust and credibility with clients and suppliers.
Threat Hunting
Proactive identification of hidden threats targeting the supply chain. Advanced analytics detect suspicious behavior before it escalates. This minimizes the impact of potential attacks on operations.
Secure Web Gateway
Web access within supply chain systems is monitored and protected. Malicious websites and phishing attempts are blocked automatically. Employees and partners can safely access cloud and internal applications.
DDoS Protection
Critical supply chain platforms are safeguarded against distributed denial-of-service attacks. Traffic surges and malicious requests are managed without disruption. This ensures availability of systems even under targeted attacks.
File Integrity Monitoring
All critical files and data in the supply chain are continuously monitored. Unauthorized changes or suspicious activity are detected immediately. This protects sensitive operational information and prevents sabotage.
Access Control Management
Suppliers and partners are evaluated for cybersecurity readiness. Weak links are identified and mitigated to reduce potential supply chain attacks. Organizations gain control over third-party risk exposure.
Access Management
Role-based access controls prevent unauthorized system or data access. Only authorized personnel can perform critical operations. This reduces the likelihood of insider threats and accidental data exposure.
Cloud Security
Cloud platforms supporting supply chain operations are continuously secured. Data, apps, and integrations are monitored to prevent breaches. Organizations can safely leverage cloud infrastructure for supply chain workflows.
IoT Security
IoT devices in warehouses, transport, and production are protected. Connected devices are monitored to prevent exploitation by attackers. This ensures smooth and secure operational processes.
API Security
APIs connecting suppliers, vendors, and internal systems are continuously monitored. Unauthorized access and data tampering are prevented. This ensures reliable and secure integrations across the supply chain.
Continuous Risk Monitoring
Supply chain systems are constantly assessed for new vulnerabilities. Emerging threats are mitigated proactively to avoid disruption. Organizations maintain resilient and secure supply chain operations.
Supply Chain Infrastructure Security Assessments
Supply chain infrastructure security assessments evaluate the overall security posture of an organization’s supply chain systems, including networks, cloud platforms, vendor connections, and operational workflows. These assessments identify vulnerabilities, misconfigurations, and potential attack paths that could disrupt operations, compromise sensitive data, or enable cyberattacks.
The assessment process includes reviewing access controls, encryption standards, API integrations, and communication channels with suppliers and partners. It also analyzes system configurations, user permissions, and third-party connections to uncover weaknesses before they can be exploited. By simulating real-world attack scenarios, organizations gain insight into their security gaps and readiness.
With these assessments, businesses receive actionable recommendations to strengthen supply chain defenses, enforce compliance with industry regulations, and protect operational continuity. The findings help reduce risks, improve resilience, and ensure that critical supply chain processes remain secure and reliable.
Process
Our Process
We follow a structured approach to secure supply chain systems and operations from cyber threats. Our process ensures resilience, compliance, and protection across suppliers, partners, and internal workflows.
Not Sure Where to Start?
Take charge of your security today. Protect your business from evolving cyber threats with confidence. Contact us now, and let’s build a stronger, safer digital future together.
Why Choose Us
We deliver end-to-end Supply Chain Security solutions that protect every link in your vendor and partner ecosystem. Our approach combines expertise, innovation, and reliability to secure sensitive data and maintain compliance. With us, you gain trusted protection and lasting peace of mind.
We Are Flexible
We adapt our security strategies to fit the unique needs of your supply chain. Our tailored approach ensures effective protection across diverse vendors and partners.
We Are on Time
We deliver assessments, monitoring, and responses promptly. Timely execution minimizes risks and keeps your supply chain running smoothly.
We Are Experts
Our team brings deep knowledge of supply chain security challenges. We apply proven methods to protect against evolving third-party threats.
We Are Reliable
We provide consistent protection and dependable support. Our reliability ensures uninterrupted business operations even during disruptions.
We Are Analytical
We carefully analyze vendor risks and vulnerabilities. Data-driven insights allow us to build effective and proactive security strategies.
We Are Innovative
We leverage modern tools and advanced methods for security. Innovation keeps your supply chain one step ahead of emerging threats.
Supply Chain Security Challenges
Third-Party Risks
Vendors, suppliers, and partners can introduce vulnerabilities into your supply chain. Weak security practices, outdated systems, or compromised accounts can be exploited by attackers. Without proper oversight, third-party risks can lead to data breaches, operational disruptions, and financial losses.
Data Theft & Leakage
Sensitive supply chain data is often shared across multiple parties. Improper handling, unsecured channels, or human error can result in confidential information being exposed. Data leakage can damage reputation, violate compliance requirements, and impact business continuity.
Operational Disruption
Cyberattacks on supply chain systems can halt production, logistics, or delivery processes. Ransomware, DDoS attacks, and system intrusions create downtime and financial loss. Ensuring continuity requires proactive monitoring and robust defenses across the entire supply chain.
IoT & System Vulnerabilities
Connected devices and integrated systems in warehouses, transportation, and production are often exploited. Weak configurations, unpatched devices, or unsecured networks increase attack surfaces. These vulnerabilities can compromise operations, data integrity, and overall supply chain security.
Industries
Industries We Serve
Our Supply Chain Security services protect businesses across industries from risks hidden in vendor and supplier networks. From finance and healthcare to manufacturing and retail, we help organizations safeguard sensitive data and maintain compliance.
Supply Chain Security Solutions
Third-Party Risk Management
We assess and continuously monitor the security posture of all vendors, suppliers, and partners. Weak links are identified and mitigation strategies are implemented to reduce exposure. By managing third-party risks, organizations can prevent breaches originating from external collaborators and maintain a secure supply chain ecosystem.
Data Protection & Encryption
Sensitive supply chain data is encrypted and access-controlled throughout its lifecycle. This prevents unauthorized access, accidental leaks, or intentional data theft. Organizations can ensure confidentiality, regulatory compliance, and trust in all digital communications and data exchanges across partners.
Operational Continuity
We implement proactive threat detection, redundancy measures, and rapid incident response plans. This ensures supply chain operations continue even under cyberattack or system disruption. Businesses benefit from minimized downtime, maintained productivity, and resilience against ransomware, DDoS, or operational threats.
IoT & System Security
Connected devices and integrated systems are monitored, patched, and secured against cyberattacks. Vulnerabilities in IoT devices or automation systems are identified and mitigated. This protects warehouses, transportation systems, and production networks from unauthorized access and operational compromise.
Steps
How We Manage and Secure Supply Chain Security
We follow a comprehensive approach to protect supply chain operations from cyber threats, disruptions, and data breaches. Our process combines proactive monitoring, robust policies, and expert guidance to ensure secure and resilient supply chain systems.
We evaluate suppliers, partners, and internal systems to identify vulnerabilities. Potential threats and weak points are highlighted for mitigation planning. This ensures visibility and control across the entire supply chain network.
Security policies, access controls, and communication rules are implemented across all supply chain systems. Role-based access ensures only authorized personnel can perform critical tasks. Policies reduce the risk of unauthorized access, misuse, or accidental data exposure.
Suppliers and partners are continuously monitored for compliance and security posture. Suspicious activity or non-compliance is flagged for immediate attention.
This prevents external breaches from affecting internal operations.
Advanced tools detect anomalies, malware, and phishing attempts targeting the supply chain. Real-time alerts allow quick action to prevent disruption. Continuous monitoring strengthens defenses against evolving cyber threats.
Email, messaging, and collaboration platforms are encrypted and monitored. Malicious links, phishing attempts, and unauthorized access are blocked. This ensures safe, reliable, and compliant communication between all parties.
Connected devices in warehouses, transportation, and production are secured. Vulnerabilities are patched, and device activity is monitored continuously. This protects operational technology from cyber exploitation and downtime.
We respond rapidly to any security incidents, contain threats, and mitigate damage. Recovery measures are implemented to restore normal operations quickly. This ensures minimal disruption to supply chain processes.
Emerging threats and vulnerabilities are evaluated regularly. Mitigation strategies are updated proactively to maintain resilience. Organizations stay ahead of potential cyberattacks affecting their supply chain.
Detailed reports track security events, incidents, and risk levels. Insights guide continuous improvement of policies and defenses. This ensures long-term security, compliance, and operational efficiency across the supply chain.
Get In Touch
Our Friendly team would love to hear from you

FAQ's
Got Questions? Find Your Answers Here!
Supply Chain Security is the practice of protecting an organization from cyber risks and vulnerabilities that may arise through vendors, suppliers, and third-party partners. It ensures safe collaboration and data protection across the entire ecosystem.
Attackers often exploit weaker links in vendor systems to access critical data. Strong supply chain security reduces the risk of breaches, ensures compliance, and safeguards business continuity.
Risks include vendor data breaches, insecure communication channels, lack of compliance, unauthorized access, and hidden vulnerabilities in third-party software or services.
Organizations can conduct vendor risk assessments, enforce compliance policies, secure data-sharing, monitor vendor activities, and implement strong incident response plans.
It should be reviewed regularly and whenever new vendors are added. Continuous monitoring combined with periodic audits ensures long-term resilience.